Cybersecurity skills shortage is worsening in Kenya amidst the raising cases of breaches according to the 6th edition of the Cyber Security Report by Serianu Limited.
“We estimate that today, Kenya needs at least 10,000 cybersecurity professionals to keep abreast with the number of organisations in need of this critical skill, yet we have observed that each year, just about 100 new personnel join the market. In another five years, going by the current rate of technology uptake, we anticipate that the country will need at least 50,000 cybersecurity professionals,” says William Makatiani CEO, Serianu Limited.
The report indicates only 1700 cybersecurity skilled professionals are certified in Kenya with 60% of companies set to experience a shortage of cybersecurity professionals in 2019, especially at senior and mid-management levels.
It confirmed that the level of cybersecurity awareness in Kenya is still low with 15% of organisations not having an established cybersecurity training program.
RELATED
“Most organisations (23%) are also still very reactive when it comes to cyber security training, these organisations train their staff only when there is an incident or problem. This is worrying considering 54% of all cyber attacks reported in the survey was through work,” reads the findings from the 2018 Cybersecurity Survey based on the feedback from over 300 IT and security professional.
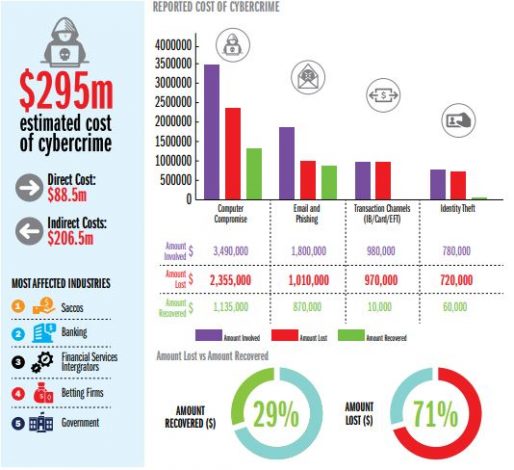
As a result, the report found out that the estimated cost of cybercrime was over USD 295 million.
Therefore, Serianu states that the skill sets required include understanding, attribution and deterrence in combating cybercrime.
“Understanding refers to the need to have a broader perspective of the events that are happening and tools being used, while attribution covers pinpointing the perpetrators. It is only then that can deterrence take place, because by now the perpetrators are known. Backed by the law, it is then easier to enforce regulations. A structured approach to assessing and addressing the cybersecurity landscape shows us our collective primary areas of focus.”